The Cyber Resilience Act: A major turning point for digital security in Europe
The Cyber Resilience Act (CRA) is the new European Union regulation that strengthens cybersecurity requirements for all digital products and connected services placed on the EU market.
An unprecedented regulatory framework
Indeed, faced with the increasing number of cyber threats and security incidents affecting consumers and businesses, the European Union has adopted a proactive and ambitious approach. Furthermore, the Cyber Resilience Act is part of this strategy to strengthen digital trust and protect European citizens. Thus, the objective is clear: to reduce cybersecurity risks in Europe and protect consumers and businesses.WHO IS AFFECTED?
- Manufacturers of digital and connected products
- Digital service providers
- Distributors and resellers
- Importers of digital products in the EU
The LCIE, your partner of today and tomorrow for the CRA.

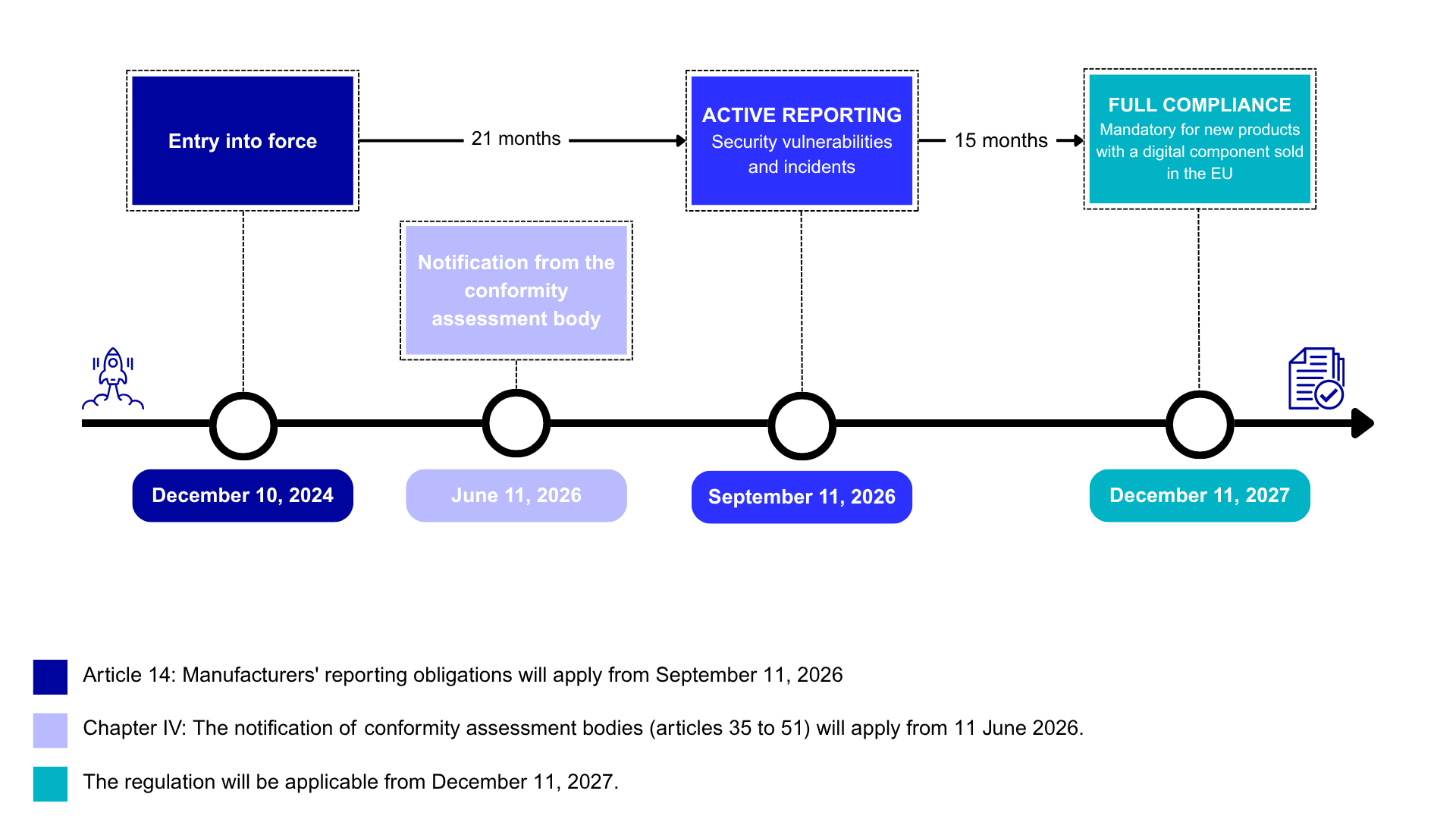
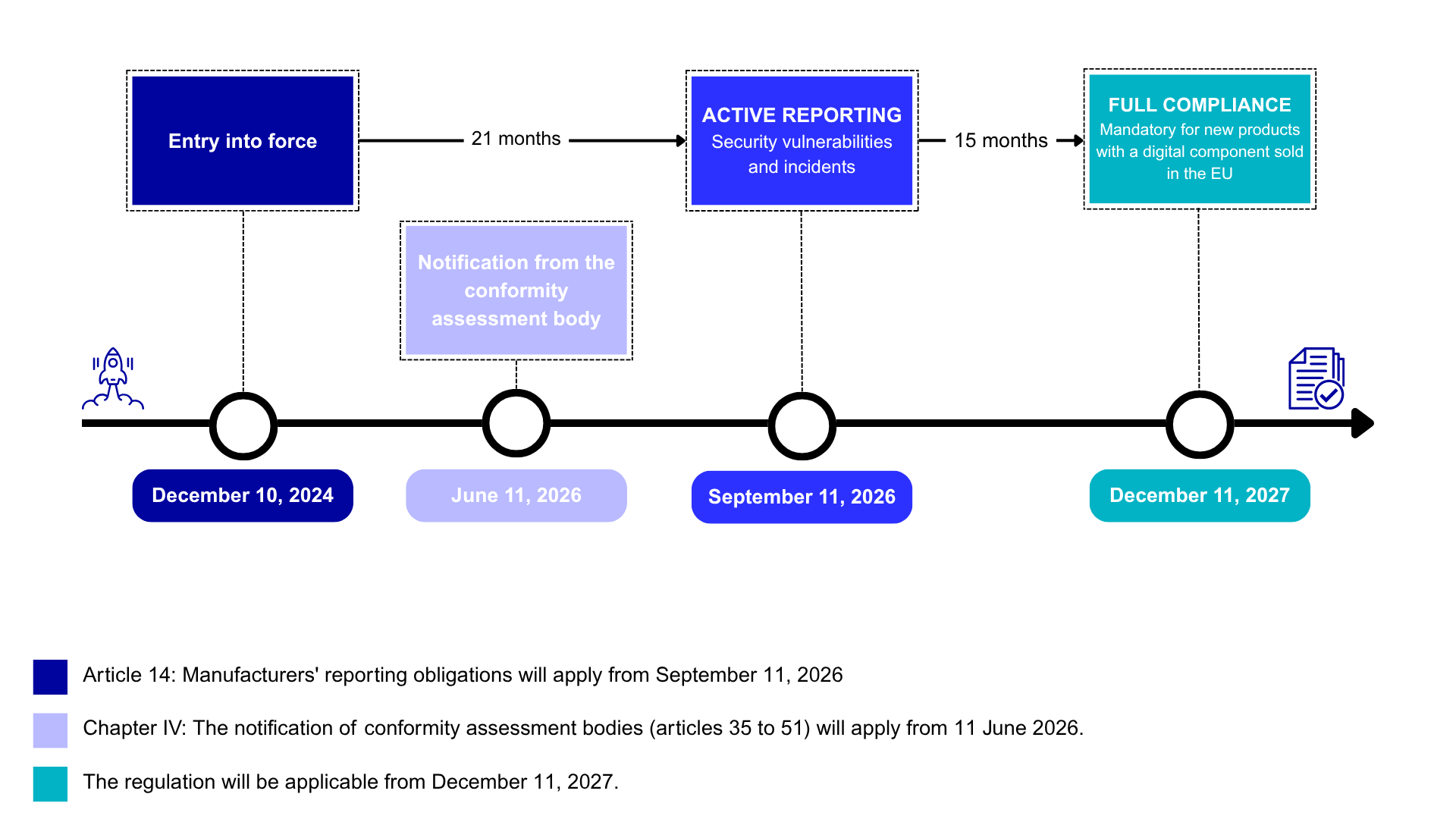
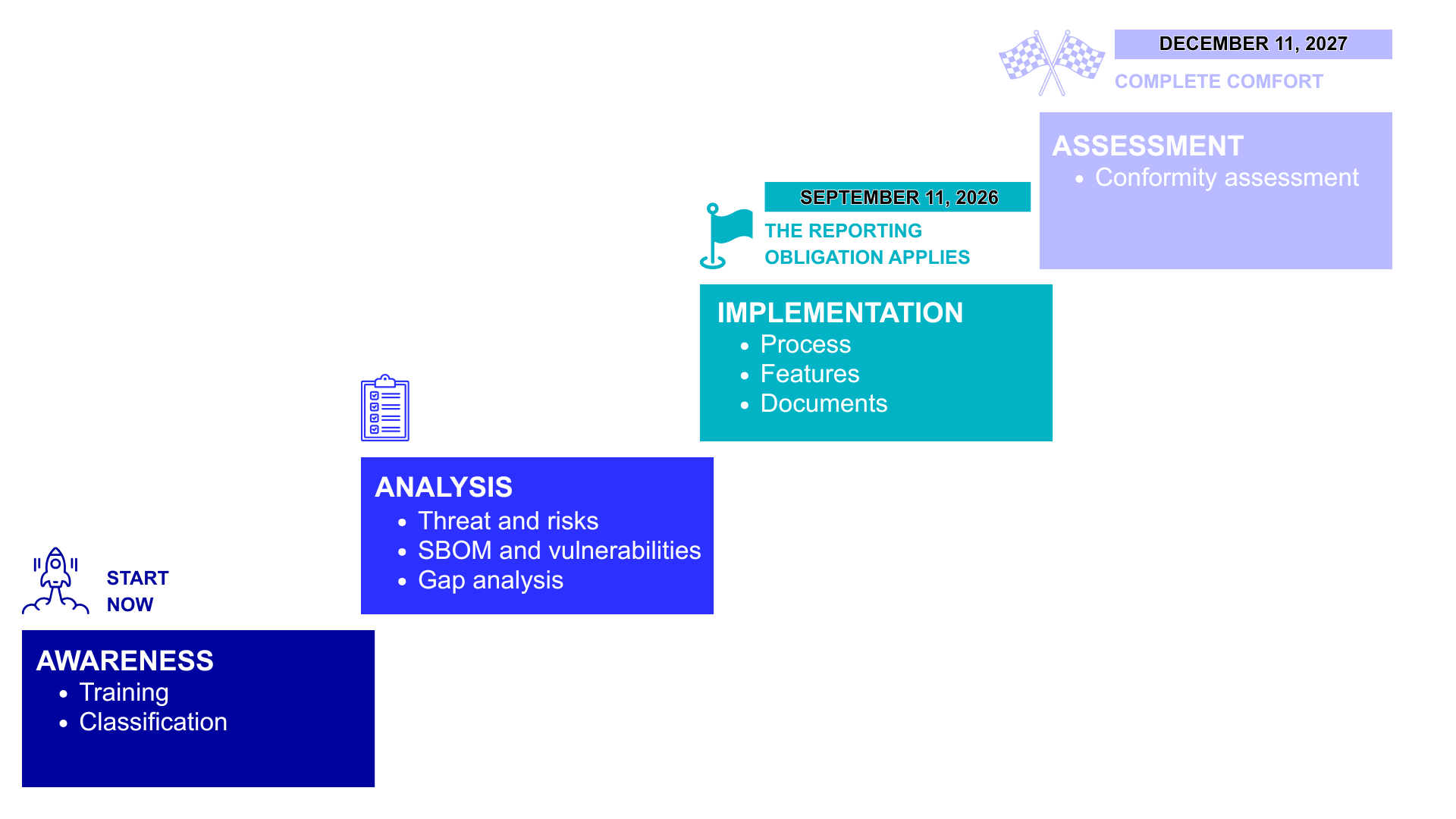
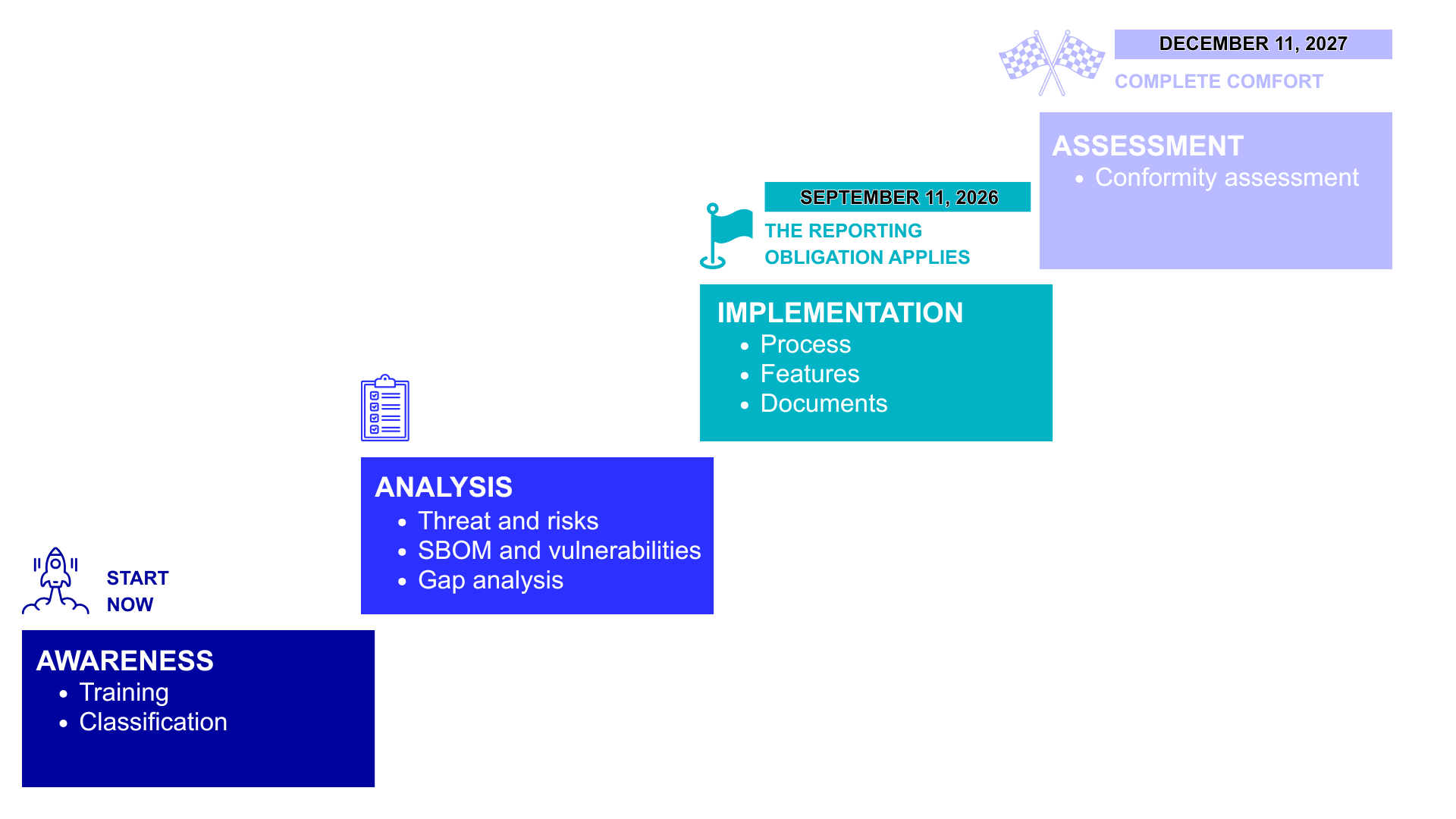
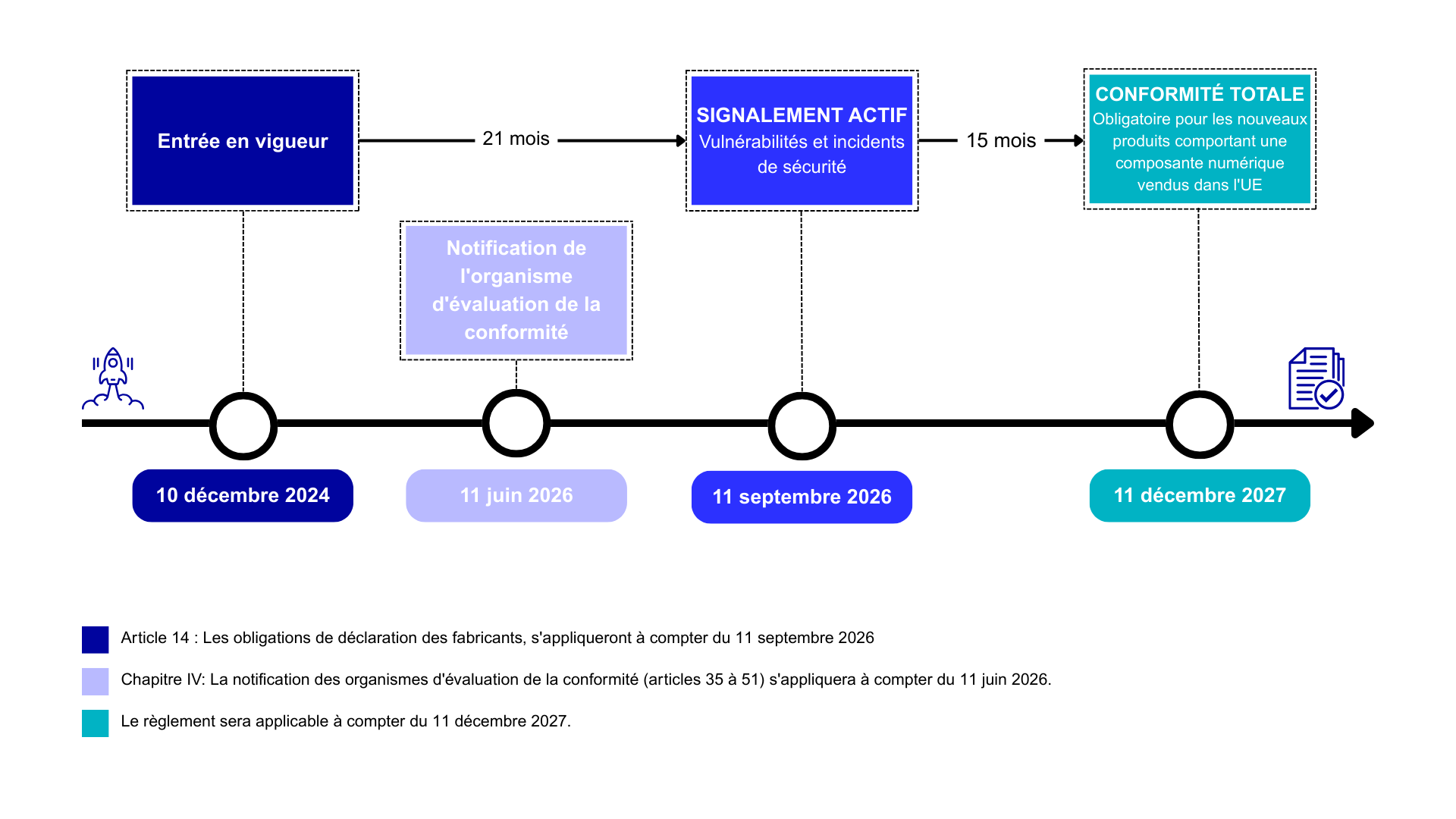
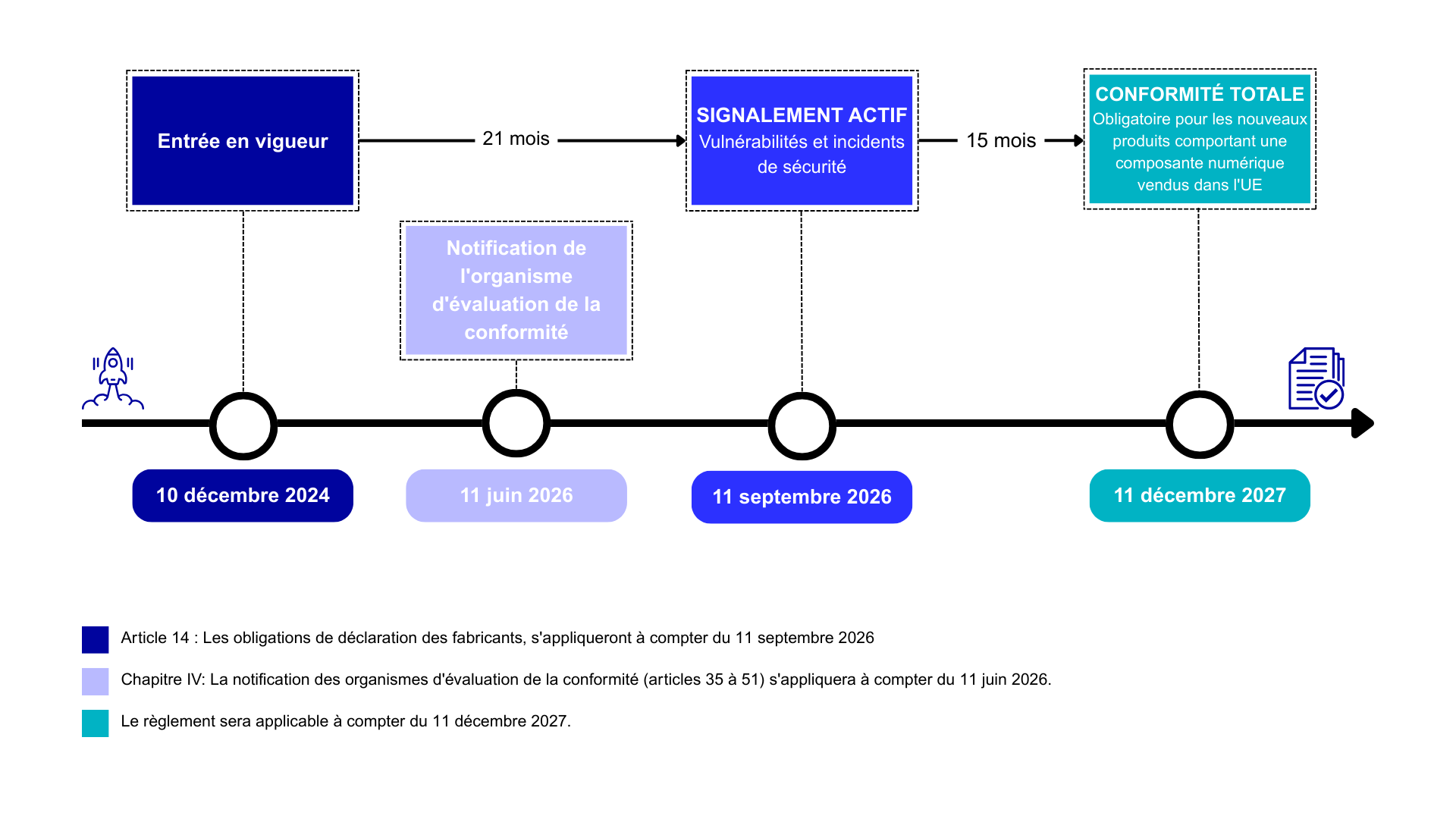
Timeline of a new regulation
Specifically, What are the requirements?
The Cyber Resilience Act (CRA) is the new European regulation that strengthens cybersecurity requirements for all digital products and connected services marketed in the EU.
Discover what these new obligations are and how they are transforming the European regulatory landscape:
- Vulnerability Management
- Configuration sécurisée
- Secure configuration
- Access control
- Confidentiality
- Integrity
- Data minimization
What standards can we rely on?
PART: PROCESS, RISK ANALYSIS
AND VULNERABILITY MANAGEMENT
- IEC 62443-4-1
- prEN 40000-1-1 (horizontal standard to come)
- prEN 40000-1-2 (horizontal standard to come)
- prEN 40000-1-3 (horizontal standard to come)
SECTION TECHNICAL SAFETY REQUIREMENTS
Pending harmonized standards (expected by the end of 2026), the use of existing standards is recommended:
- IEC 62443-4-2 with good coverage of requirements
- ETSI EN 303 645 with good coverage of requirements
- EN 18031 with less coverage
WHICH PRODUCTS ARE AFFECTED?
- Software
- Materials
- Cloud services
- Connected objects
- Connected systems
product classification
   |
|
|
Default Category- self-assessment |
   |
Important products : application of standards/third-party assessment
|
|
   |
Critical Products : third-party evaluation (and potentially certification in the future)
|
|
   |
Free and open source software (FOSS) : self-assessment (unless they are categorized as "critical products") |
our cybersecurity services
- CLASSIFY YOUR PRODUCTS : Precisely determine the regulatory applicability and classification of your products according to the applicable regulatory frameworks. This foundational step ensures that you apply the correct requirements from the outset and avoids costly compliance errors.
- TRAINING: We offer training courses led by professionals on cybersecurity for medical devices and industrial systems, the Cyber Resilience Act, and penetration testing.
Download our 2026 training catalogue in French to find out more. - STRUCTURE YOUR EVALUATION: Update or create a comprehensive and documented product risk assessment methodology tailored to your industry and specific needs. A structured approach allows for the systematic identification of hazards and the objective and traceable assessment of risks.
- IDENTIFY THE DISCREPANCY: Conduct a thorough gap analysis between your current situation and the requirements of the selected standard. This comparative assessment highlights non-conformities, their criticality, and priority areas for improvement to achieve full compliance.
- PLAN YOUR TRANSITION: Develop a realistic and progressive compliance roadmap, with clear milestones, defined responsibilities, and allocated resources. A structured plan facilitates project management and ensures controlled compliance within the given timeframe.
- VALIDATE CONFORMITY : Formally and comprehensively assess your products' compliance with the requirements of the relevant regulatory authorities. This final validation demonstrates your commitment to quality and safety, and constitutes documented proof of your regulatory compliance.
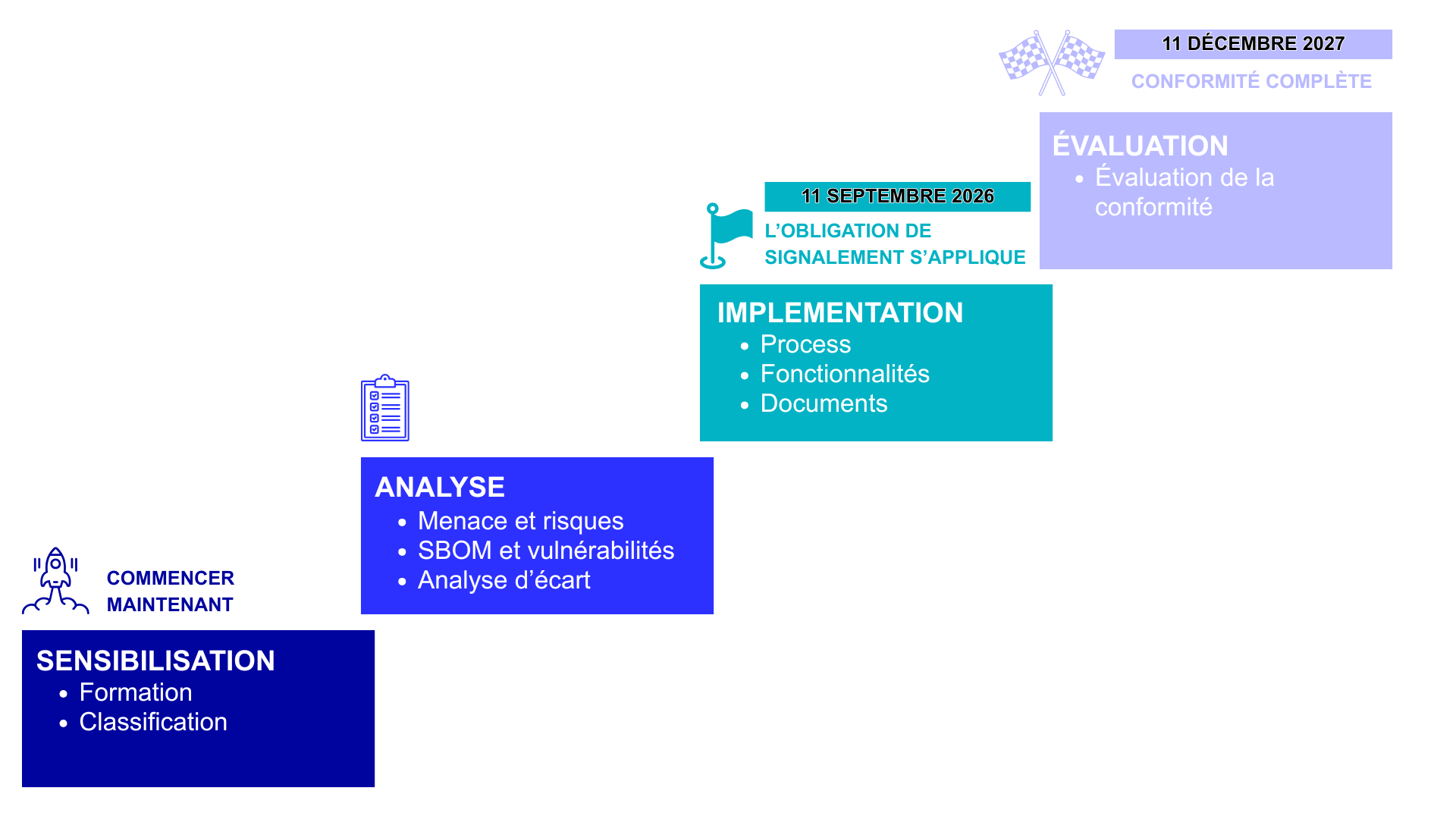
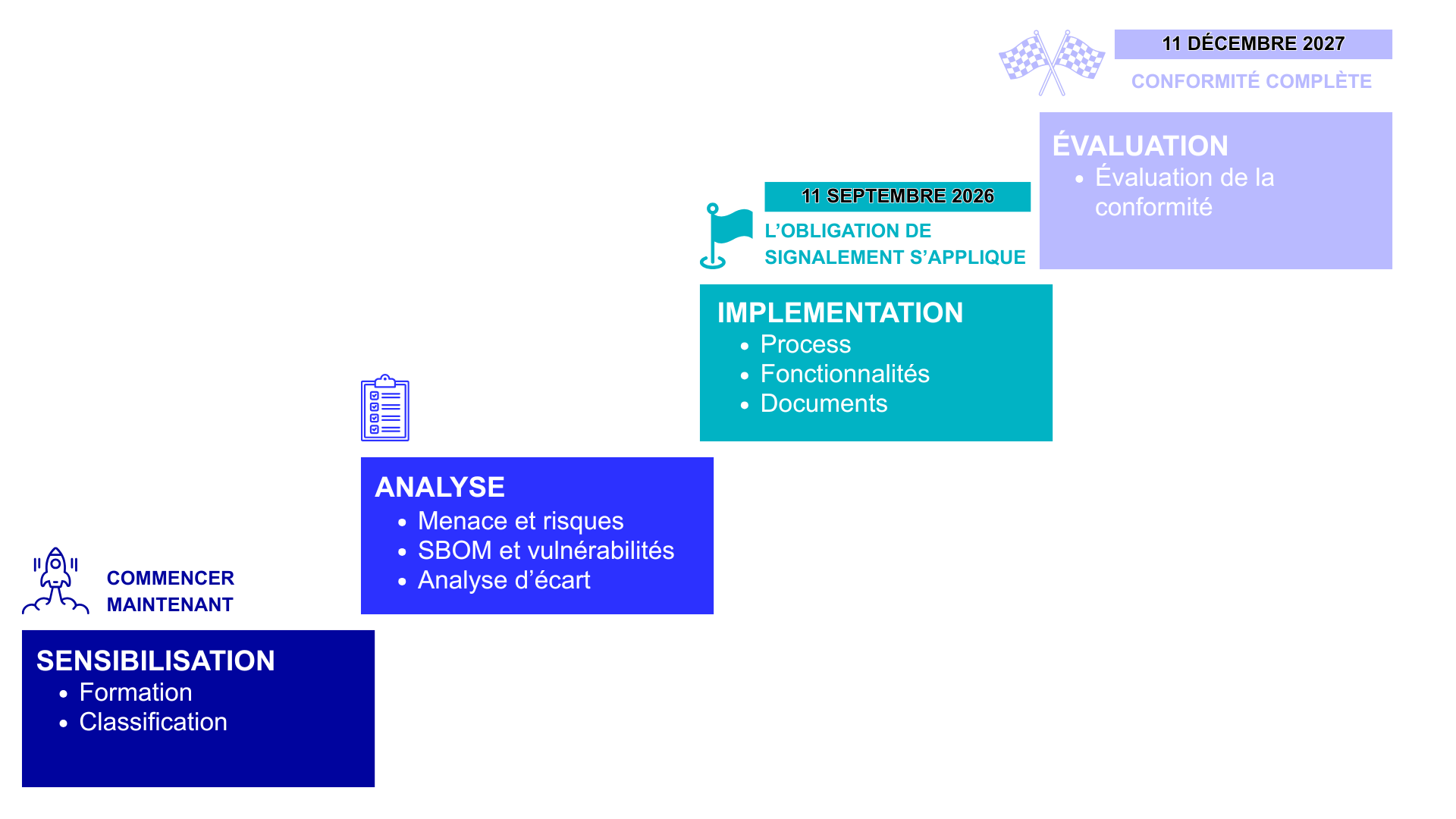
CRA ROADMAP - STEPS TOWARDS COMPLIANCE
Why choose LCI?
|
Leader on IEC 62443
|
Experts ready to listen to you
|
A committed team
|
ALSO READ: EUCC – A NEW CYBERSECURITY SYSTEM FOR ICT PRODUCT CERTIFICATION IN EUROPE
The European Cybersecurity Certification (EUCC) represents a new approach to the certification of information and communication technology (ICT) products in Europe.
The EUCC is based on the Common Criteria (CC) certification system, which incorporates innovative concepts recognized internationally to meet the needs of stakeholders, including improved provisions for patch management, vulnerability management and vulnerability disclosure in certified products.



Join the CRA movement and propel your business to the forefront of the European scene! Winning regulations for products that stand out.
I would like to request contact or a quote
related pages:


CRA | Le Cyber Resilience Act
Le Cyber Resilience Act : Un tournant majeur pour la sécurité numérique en Europe
La loi sur la cyber-résilience (Cyber Resilience Act - CRA) est le nouveau règlement de l'Union européenne qui renforce les exigences en matière de cybersécurité pour tous les produits numériques et services connectés mis sur le marché de l'UE.
Un cadre réglementaire sans précédent
En effet, face à la multiplication des cybermenaces et des incidents de sécurité affectant les consommateurs et les entreprises, l'Union Européenne a adopté une approche proactive et ambitieuse. Par ailleurs, le Cyber Resilience Act s'inscrit dans cette stratégie de renforcement de la confiance numérique et de protection des citoyens européens.Ainsi, l'objectif est clair : réduire les risques de cybersécurité en Europe et protéger les consommateurs ainsi que les entreprises.
QUI EST CONCERNÉ ?
- Les fabricants de produits numériques et connectés
- Les fournisseurs de services numériques
- Les distributeurs et revendeurs
- Les importateurs de produits numériques dans l'UE
Le LCIE, votre partenaire d'aujourd’hui et de demain pour le CRA.



chronologie d'une nouvelle règlementation
CONCRÊTEMENT, QUELLES SONT LES EXIGENCES ?
Le Cyber Resilience Act (CRA) est le nouveau règlement européen qui durcit les exigences en matière de cybersécurité pour tous les produits numériques et services connectés commercialisés dans l'UE.
Découvrez quelles sont ces nouvelles obligations et comment elles transforment le paysage réglementaire Européen :
- Gestion des vulnérabilités
- Configuration sécurisée
- Mise à jour de sécurité
- Contrôle d'accès
- Confidentialité
- Intégrité
- Minimisation des données
Sur quels standards peut-on s'appuyer ?
PARTIE PROCESS, ANALYSE DE RISQUES
ET GESTION DES VULNÉRABILITÉS
- L'IEC 62443-4-1
- prEN 40000-1-1 (standard horizontal à venir)
- prEN 40000-1-2 (standard horizontal à venir)
- prEN 40000-1-3 (standard horizontal à venir)
PARTIE EXIGENCES TECHNIQUES DE SÉCURITÉ
En attendant les standards harmonisés (attendus pour fin 2026), une utilisation des standards existants est préconisée :
- L'IEC 62443-4-2 avec une bonne couverture des exigences
- L'ETSI EN 303 645 avec une bonne couverture des exigences
- L'EN 18031 avec une couverture moindre
QUELS SONT LES PRODUITS CONCERNÉS ?
- Les logiciels
- Le matériel
- Les services cloud
- Les objets connectés
- Les systèmes connectés
classification des produits
   |
|
|
Catégorie par défaut - auto-évaluation |
   |
Produits importants : application des normes/évaluation par un tiers
|
|
   |
Produits critiques : évaluation par un tiers (et potentiellement certification à l’avenir)
|
|
   |
Logiciels libres et open source (FOSS) : auto-évaluation (sauf s'ils sont catégorisés comme « produits critiques ») |
nos services cybersécurité
- CLASSIFIER VOS PRODUITS : Déterminer précisément l'applicabilité réglementaire et la classification de vos produits en fonction des cadres normatifs applicables. Cette étape fondatrice garantit que vous appliquez les bonnes exigences dès le départ et évite les erreurs de conformité coûteuses.
- FORMER : nous vous proposons des formations dispensées par des professionnels, sur la cybersécurité des dispositifs médicaux ou systèmes industriels, le Cyber Resilience Act, ou encore les pentests. Téléchargez notre catalogue de formations 2026 pour en savoir plus.
- STRUCTURER VOTRE ÉVALUATION : Mettre à jour ou créer une méthodologie complète et documentée d'évaluation des risques produits, adaptée à votre secteur d'activité et à vos spécificités. Une approche structurée permet d'identifier systématiquement les dangers et d'évaluer les risques de manière objective et traçable.
- IDENTIFIER LES ÉCARTS : Effectuer une analyse approfondie des écarts entre votre situation actuelle et les exigences de la norme sélectionnée. Cette évaluation comparative met en lumière les non-conformités, leur criticité et les domaines prioritaires d'amélioration pour atteindre la conformité totale.
- PLANIFIER VOTRE TRANSITION : Élaborer une feuille de route de conformité réaliste et progressive, avec des jalons clairs, des responsabilités définies et des ressources allouées. Un plan structuré facilite le pilotage du projet et assure une mise en conformité maîtrisée dans les délais impartis.
- VALIDER LA CONFORMITÉ : Évaluer formellement et exhaustivement la conformité de vos produits aux exigences des Autorités de Régulation Compétentes. Cette validation finale démontre votre engagement envers la qualité et la sécurité, et constitue la preuve documentée de votre conformité réglementaire.
FEUILLE DE ROUTE CRA - LES ÉTAPES VERS LA CONFORMITÉ
pourquoi choisir le lcie ?
|
Leader sur l'IEC 62443
|
Des experts à votre écoute
|
Une équipe engagée
|
A LIRE ÉGALEMENT : EUCC – UN NOUVEAU SYSTÈME DE CYBERSÉCURITÉ POUR LA CERTIFICATION DES PRODUITS TIC EN EUROPE
La Certification européenne de cybersécurité (EUCC) représente une nouvelle approche de la certification des produits des technologies de l’information et de la communication (TIC) en Europe.
L’EUCC est fondé sur le système de certification des Critères Communs (CC), qui intègre des concepts novateurs reconnus au niveau international pour répondre aux besoins des parties prenantes, notamment des dispositions améliorées pour la gestion des correctifs, la gestion des vulnérabilités et la divulgation des vulnérabilités dans les produits certifiés.



Rejoignez le mouvement CRA et propulsez votre activité sur le devant de la scène européenne ! Une réglementation gagnante pour des produits qui se démarquent.
Je souhaite faire une demande de contact ou de devis
pages connexes :





