
Certification of IoT devices
IoT CERTIFICATION SYSTEM
LCIE Bureau Veritas has developed its own reference and certification system to help IoT device manufacturers develop state of the art cybersecurity products that can benefit from an official label that consumers recognize.
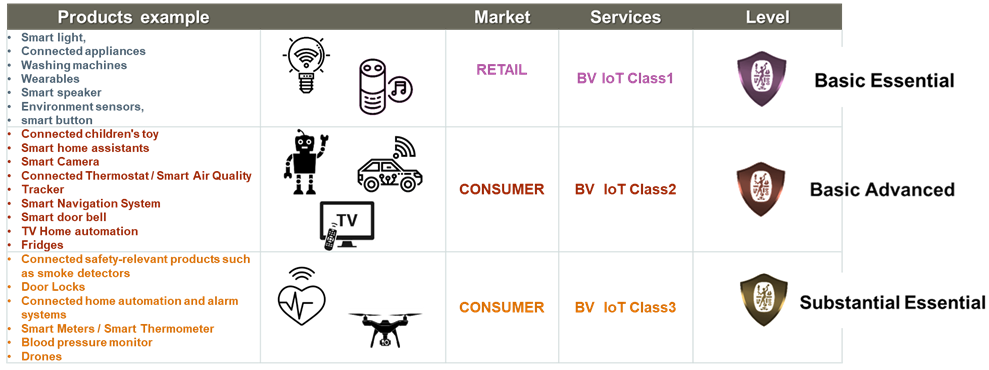
To cover the wide range of consumer IoT devices, 3 classes of security requirements have been defined as part of the BV IoT certification system, leading to 3 different security levels and labels.
15 security categories have been defined to represent state of the art cybersecurity manufacturing
- Passwords management
- Keep software up to date
- Securely store sensitive data
- Minimize exposed attack surfaces
- Thee inital state is secure
- Administrator and user guidance analysis
- Third-party components management
- Unique reference of the device
- Resistance to know vulnerabilities
- Authentification and access controls
- Protection of data in transit
- Data input validity
- Personnal data management
- Secure boot
- Protection of data at rest
CTIA IOT
CTIA IoT Cyber Security certification confirms that certified IoT devices (cellular and Wi-Fi enabled) meet a security standard defined by the certification program. By verifying the cybersecurity functions of an IoT device, manufacturers are creating a foundation for a secure smart home, smart city, connected cars, and other IoT applications and products.
As a cybersecurity certification test laboratory for IoT devices approved by the CTIA under the CTIA Authorized Test Laboratory (CATL) program, we support you in the certification of your IoT devices.
CYBERSECURITY ACT
The “Cybersecurity Act” was defined in 2019 in Europe to cover cybersecurity certification systems that will be applicable across 3 levels: High, Substantial, and Basic.
The RED directive is in the process of incorporating requirements that would cover “basic” cybersecurity for connected objects, which will be applicable starting in 2021.
The classification of “Bureau Veritas cybersecurity certification for IoT devices” was designed to verify that the product has taken into account the key minimum requirements from these regulations.
- A secure configuration out of the box
- Signed code and secured updates
- Protection against exploitation from known failures and vulnerabilities.
- Personal data management
LCIE Bureau Veritas can also individually verify the “Management of personal data”
- Consumers will be informed regarding the management and processing of their personal data
- Consumers must give their consent
- Consumers have the option to delete their personal data


